
CATEGORIES:
BiologyChemistryConstructionCultureEcologyEconomyElectronicsFinanceGeographyHistoryInformaticsLawMathematicsMechanicsMedicineOtherPedagogyPhilosophyPhysicsPolicyPsychologySociologySportTourism
To prevent faulty network devices from carrying dangerous voltage levels, equipment must be grounded correctly
18. A network engineer is measuring the transfer of bits across the company backbone for a mission critical database application. The engineer notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)
the amount of traffic that is currently crossing the network*
the sophistication of the encapsulation method applied to the data
the type of traffic that is crossing the network*
the latency that is created by the number of network devices that the data is crossing*
the bandwidth of the WAN connection to the Internet
the reliability of the gigabit Ethernet infrastructure of the backbone
19. What is a possible hazard that can be caused by network cables in a fire?
The cable insulation could be flammable.*
Users could be exposed to excessive voltage.
Network cables could be exposed to water.
The network cable could explode.
20. What device is commonly used to verify a UTP cable?
a multimeter
an Optical Time Domain Reflectometer
a cable tester*
an ohmmeter
21. What needs to be checked when testing a UTP network cable?
capacitance
wire map*
inductance
flexibility
22. Refer to the exhibit. A ping to PC2 is issued from PC0, PC1, and PC3 in this exact order. Which MAC addresses will be contained in the S1 MAC address table that is associated with the Fa0/1 port?

just PC0 and PC1 MAC addresses*
just the PC0 MAC address
PC0, PC1, and PC2 MAC addresses
just the PC1 MAC address
just the PC2 MAC address
23. Which function is provided by TCP?
data encapsulation
detection of missing packets*
communication session control
path determination for data packets
24. What does a router use to determine where to send data it receives from the network?
an ARP table
a routing table*
the destination PC physical address
a switching table
25. Which router interface should be used for direct remote access to the router via a modem?
an inband router interface
a console port
a serial WAN interface
an AUX port*
26. A technician is configuring a router to allow for all forms of management access. As part of each different type of access, the technician is trying to type the command login. Which configuration mode should be entered to do this task?
user executive mode
global configuration mode
any line configuration mode*
privileged EXEC mode
27. Which three statements characterize the transport layer protocols? (Choose three.)
TCP and UDP port numbers are used by application layer protocols.*
TCP uses port numbers to provide reliable transportation of IP packets.
UDP uses windowing and acknowledgments for reliable transfer of data.
TCP uses windowing and sequencing to provide reliable transfer of data.*
TCP is a connection-oriented protocol. UDP is a connectionless protocol.*
28. Refer to the exhibit. A TCP segment from a server has been captured by Wireshark, which is running on a host. What acknowledgement number will the host return for the TCP segment that has been received?
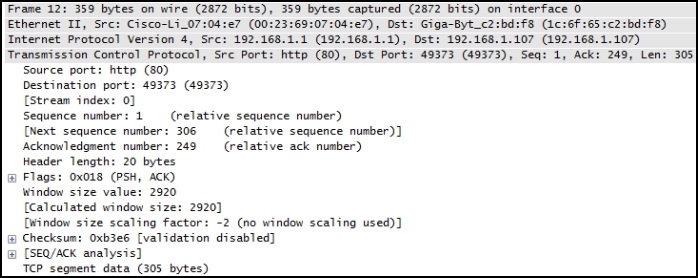
306*
29. Which statement is true about an interface that is configured with the IPv6 address command?
IPv6 traffic-forwarding is enabled on the interface.
A link-local IPv6 address is automatically configured on the interface.*
A global unicast IPv6 address is dynamically configured on the interface.
Any IPv4 addresses that are assigned to the interface are replaced with an IPv6 address.
30. Refer to the exhibit. The network administrator for a small advertising company has chosen to use the 192.168.5.96/27 network for internal LAN addressing. As shown in the exhibit, a static IP address is assigned to the company web server. However, the web server cannot access the Internet. The administrator verifies that local workstations with IP addresses that are assigned by a DHCP server can access the Internet, and the web server is able to ping local workstations. Which component is incorrectly configured?

subnet mask
DNS address
host IP address
default gateway address*
31. Refer to the exhibit. An administrator must send a message to everyone on the router A network. What is the broadcast address for network 172.16.16.0/22?
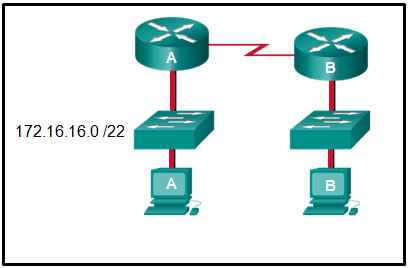
172.16.16.255
172.16.20.255
172.16.19.255*
172.16.23.255
172.16.255.255
32. A network administrator is variably subnetting a given block of IPv4 addresses. Which combination of network addresses and prefix lengths will make the most efficient use of addresses when the need is for 2 subnets capable of supporting 10 hosts and 1 subnet that can support 6 hosts?
10.1.1.128/28
10.1.1.144/28
10.1.1.160/29********
10.1.1.128/28
10.1.1.144/28
10.1.1.160/28
10.1.1.128/28
10.1.1.140/28
10.1.1.158/26
10.1.1.128/26
10.1.1.144/26
10.1.1.160/26
10.1.1.128/26
10.1.1.140/26
10.1.1.158/28
33. How many additional bits should be borrowed from a /26 subnet mask in order to create subnets for WAN links that need only 2 useable addresses?
4*
34. A logical topology influences the type of network framing and media access control that will be used.
35. Refer to the exhibit. The administrator configured the access to the console and the vty lines of a router. Which conclusion can be drawn from this configuration?

Unauthorized individuals can connect to the router via Telnet without entering a password.
Because the IOS includes the login command on the vty lines by default, access to the device via Telnet will require authentication.*
Access to the vty lines will not be allowed via Telnet by anyone.
Because the login command was omitted, the password cisco command is not applied to the vty lines.
36. An administrator issued the service password-encryption command to apply encryption to the passwords configured for enable password, vty, and console lines. What will be the consequences if the administrator later issues the no service password-encryption command?
It will remove encryption from all passwords.
It will reverse only the vty and console password encryptions.
It will not reverse any encryption.*
It will reverse only the enable password encryption.
37. After making configuration changes, a network administrator issues a copy running-config startup-config command in a Cisco switch. What is the result of issuing this command?
The new configuration will be stored in flash memory.
The new configuration will be loaded if the switch is restarted.*
The current IOS file will be replaced with the newly configured file.
The configuration changes will be removed and the original configuration will be restored.
38. What are two features of ARP? (Choose two.)
If a host is ready to send a packet to a local destination device and it has the IP address but not the MAC address of the destination, it generates an ARP broadcast.*
An ARP request is sent to all devices on the Ethernet LAN and contains the IP address of the destination host and its multicast MAC address.
When a host is encapsulating a packet into a frame, it refers to the MAC address table to determine the mapping of IP addresses to MAC addresses.
If no device responds to the ARP request, then the originating node will broadcast the data packet to all devices on the network segment.
If a device receiving an ARP request has the destination IPv4 address, it responds with an ARP reply.*
39. What are two examples of the cut-through switching method? (Choose two.)
store-and-forward switching
fast-forward switching*
CRC switching
fragment-free switching*
QOS switching
40. A network administrator is enabling services on a newly installed server. Which two statements describe how services are used on a server? (Choose two.)
Data sent with a service that uses TCP is received in the order the data was sent.
A port is considered to be open when it has an active server application that is assigned to it.*
An individual server can have two services that are assigned to the same port number.
An individual server cannot have multiple services running at the same time.
Server security can be improved by closing ports that are associated with unused services.*
41. Why does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
to identify the broadcast address of the destination network
to identify the host address of the destination host
to identify faulty frames
to identify the network address of the destination network*
42. Given the binary address of 11101100 00010001 00001100 00001010, which address does this represent in dotted decimal format?
234.17.10.9
234.16.12.10
236.17.12.6
236.17.12.10*
43. A particular telnet site does not appear to be responding on a Windows 7 computer. What command could the technician use to show any cached DNS entries for this web page?
ipconfig /all
arp -a
ipconfig /displaydns*
nslookup
Fill in the blank.
Date: 2015-12-18; view: 4225