
CATEGORIES:
BiologyChemistryConstructionCultureEcologyEconomyElectronicsFinanceGeographyHistoryInformaticsLawMathematicsMechanicsMedicineOtherPedagogyPhilosophyPhysicsPolicyPsychologySociologySportTourism
WHY PEOPLE SURF THE NET
There are so many things you can do and participate in once connected to the (a)_______. They include using a range of services to (b)______ and share information and things quickly and inexpensively with tens of millions of people, both young and old and from diverse (c) _______ around the world. For example:
· You’ll be able to keep in touch and send things to (d) ____ and friends using (e) ____, Internet telephone, (f) _____ and video conferencing.
· You can also tap into thousands of databases, online libraries and newsgroup around the world to gather information on any (g)_____ of interest for work or recreation. The information can be in the form of text, pictures or even (h)_____.
· This means you can stay (i) __ with news, sports, weather and any current affairs around the world with information (j) ______ daily, hourly or instantly.
· You can also locate and download computer software and other products that are available in (k)__.
· You can listen to (l)____, and watch (m)_____.
· There is also a growing number of (n)________ games and (o)_____ tools.
And as well as using the Internet for receiving things, you will be able to (p) _______ information about your school and hobbies.
Find in the text:
a) Where you have to be connected to if you want to participate in a chatroom.
b) How you can communicate with people from all over the world.
c) Which sites you tap into when you are doing research on any topic.
d) Where you can find information about books.
Use your dictionary to find the meaning of up-to-date, update, out of date, outdated.
Then fill in the blanks with the suitable word.
a) Kevin bought an …. version of the software. It’s much better than the previous one.
b) We are having great trouble in … our database.
c) That software is so … I really think you should buy the new version.
d) Nowadays this technique is rather ….
Based on both texts (A and B), write about the advantages and disadvantages of the Internet. You may add others besides the ones mentioned in the texts.
3. VOCABULARY EXERCISES
A. Are you a computer expert?
| Webcam | Trash |
| Powerpoint | Monitor |
| Firefox | Yahoo |
| CD-ROM | Internet Explorer |
| Keyboard | Hard-drive |
| Scanner | Printer |
| Excel | Floppy disc |
| Word | ipod |
B. Now use the words to fill in the spaces in these sentences.
| search engine download browser kilobyte cookie portal | search term subscription URL pop-up banner modem |
Начало формы
1. Did you see that ___on the CNN site yesterday? It was for a children's charity and looked interesting so I clicked on it.
2. I don't like visiting sites where there are too many ___ . It takes me so long to close them all!!
3. Many people ____songs off the internet and listen to them on their computers.
4. "Is the _____of the BBC bbc.com or bbc.co.uk?" "The second one I think."
5. My computer is working perfectly but my ____is broken so I can't access the internet at all.
6. I found a great site about butterflies yesterday but now I can't find it again. I went to Google and typed in the ____"amazon butterflies" but I don't remember which one it was.
7. Sometimes if you look at a website with Internet Explorer and then open up a different ____, the site will look very different.
8. This photo is taking too long to load, it is over 800 ___. I think I will see it when I have more time.
9. I like that website but now they want everyone to pay a ____of $20 a month so I will go and find a free site elsewhere.
10. We found a great internet _____yesterday that I'd never seen before. You can have an e-mail account, get news about your favourite sport and even use their chat rooms. And it has a search function too.
11. Amazon uses _____ a lot which means they can give you a personal welcome back message every time you visit their site.
12. The biggest _____on the internet is Google but Yahoo and MSN are popular too.
4. USING THE INTERNET
Complete this extract from a guide to using the Internet with the following:
| on-line | web page | sites |
| chat room | download | newsgroup |
The World Wide Web is made up of millions of (1) …… created by anybody from multimedia corporations to ordinary people like you and me. On the web you can read (2) …. Newspapers or magazines; you can watch videos, (3) …. Music or buy anything from a CD to a holiday. You can go into a (4)…….. and talk to other people all over the world or join a (5)…. for more serious debate. If you are really ambitious you might even like to try creating your own (6) ….. . Then you can show your holiday pictures to the whole world!
5.  READING
READING
Celebrities like Angelina Jolie try to make people aware that differences still exist between those with access to information and those without.
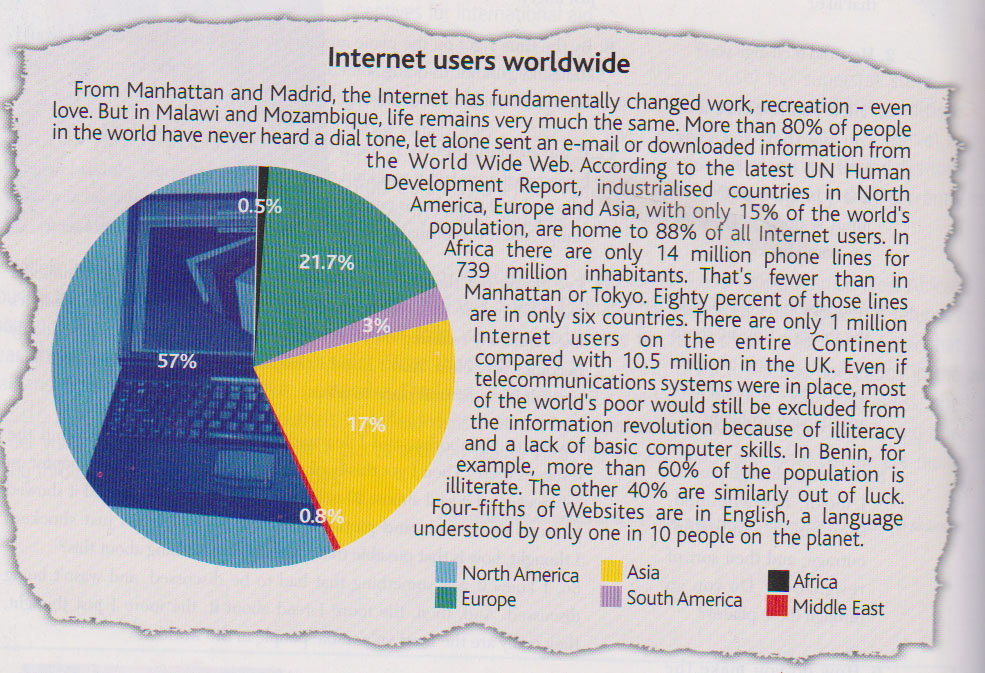
There is a gap between those individuals and those communities that have do not have access to the information technologies that are transforming our lives.
This gap is the digital divide.
Being on the privileged side of the divide means new jobs, access to education, new modes of community building, ease of access to global markets and to computers and telecommunication networks. Who is on which side of the divide? Look at the graph below and read the text to find out.

6. SPEAKING
Do you agree with the statement below? Does the Net and virtual friendships cause this feeling of isolation among tens? Explain.
“The Internet is your friend but it shouldn’t be your only friend”

 Lesson 43.
Lesson 43.
1. SPEAKING
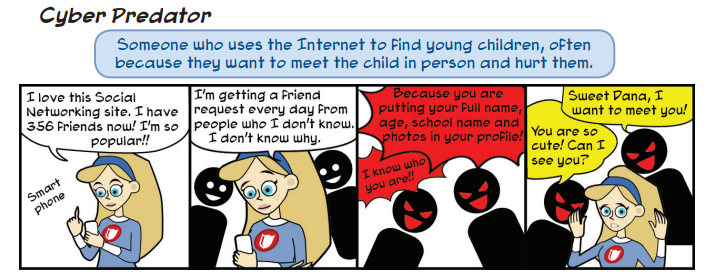
Comment on the cartoon:
 2. READING
2. READING
Read the following text.
THE NET
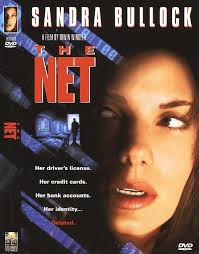 Her driver’s license, her credit cards, her bank accounts, her identity, deleted!
Her driver’s license, her credit cards, her bank accounts, her identity, deleted!
Like all of us, Angela Bennett (Sandra Bullock) lives in the age of information on the privileged side of the divide. Every trace of her existence is computerized. Everything about her is encoded somewhere on a complex network of information. It’s something Angela had never thought about … until the day she was deleted.
With the explosion of technological advances in the last few years, The Net is a story virtually torn from today’s headlines. It takes place in a world in which anything, from ordering a pizza to retrieving records from half-way across the planet, can be accomplished through the vast and complicated map of phone lines and computers known as the Internet; a world in which, with the right knowledge and the right program, a good hacker can log into remote computers and alter any information they choose: flight plans, medical and criminal records, top secret government information, even someone’s identity …
Sandra Bullock stars as Angela Bennett, Cathedral Systems’ top analyst. As a well-paid freelancer, she spends her days ironing out bugs in games designed for adolescent boys or tracking down viruses hacked into unsuspecting systems, and her nights “chatting” with other shy cyber-jockeys on the Net. She’s quite happy with her sheltered, if somewhat lonely routine … until the very life she’s made for herself pushes her headlong into the middle of a murderous web of corruption and conspiracy.
A. Read the definitions below. Choose the one which best suites each word in bold in the text
a) eliminated; made invisible;
b) faults or defects in a system;
c) stored, processed and analysed by computer;
d) software programmes capable of causing great harm to files and computer programmes;
e) become connected;
f) a programmer who breaks into computer systems in order to steal, change or destroy information;
g) converted from normal language into a code.
1.  SPEAKING
SPEAKING
According to you, does the Internet have the potential to make people’s lives easier, or is it as dangerous as the plot of the film may suggest? Not down your opinions and then compare your conclusions with those of your classmates.
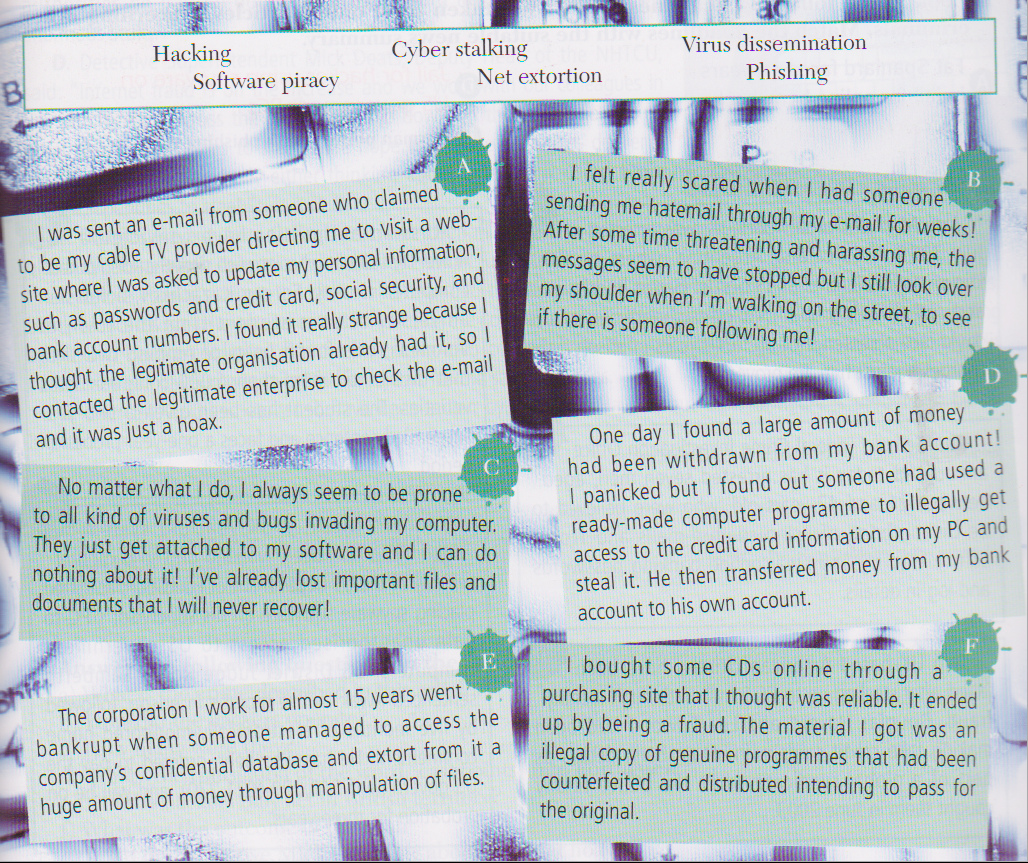
 CYBER CRIMES
CYBER CRIMES
Cyber crime consists of:
· Specific crimes dealing with computers and networks (such as hacking);
· the facilitation of traditional crime through the use of computers (Internet fraud);
· the use of computers by criminals for communication and document or data storage (“computer-supported crime”)
2.  READING: VICTIMS OF CYBER CRIMES
READING: VICTIMS OF CYBER CRIMES
All of the following statements report stories of people who have been victims of cyber crimes.
Read the texts and identify the crime that was committed (choose from the ones in the box below)
Explain in your own words the meaning of the cyber crimes you have just identified.
3. SAFETY TIPS
There are some tips you should follow to protect yourself from online hackers. Match both halves of the sentences to build meaningful pieces of advice.
| 1. Use of the latest version of a good anti-virus software package | a. which should combine upper and lower case characters. |
| 2. Use the latest version of | b. for different websites. |
| 3. Don’t open e-mail attachments | c. and do not go to websites from e-mail links. |
| 4. Confirm the sites you are doing business with | d. which allows upgrading from the Internet. |
| 5. Create password containing at least 8 digits | e. unless you know the source. |
| 6. Use different passwords | f. only to secure sites. |
| 7. Send credit card information | g. the operating system, web browsers and e-mail programmes. |
Which of the security tips mentioned above do you follow?
4.  READING: SAFETY LESSONS
READING: SAFETY LESSONS
Read the following article by Mark Prigg.
UK CHILDREN GET SAFETY LESSONS ON NET PREDATORS
Children will be given safety on the Net.
Every secondary school pupil in Britain is to be given Internet safety lessons, starting today.
They will see two hard-hitting video showing the effects of online grooming and abduction and receive safety talks and practical sessions.
It is hoped that about a million 11 to 16 –year-olds will attend the “ThinkuKnow” scheme being run by police, teachers and social services staff backed by the Home Office. The service will be run by the Child Exploitation and Online Protection Centre, which is backed by the Government and was set up in April 2006 to act as a point of contract for organizations investigating the abuse of children on the Net.
A website, www.thinkuknow.co.uk, has been set up where children can report instances of abuse to the police. It will give advice on blogs and news sites and there will be a range of online games. “The Government is determined to do everything it can to protect children from predatory paedophiles, including those who use the Internet and other communication technologies,” said Home Office Minister, Vernon Coaker.
 An overhaul of the law saw increased penalties for online paedophiles following the case of a former US marine who groomed a 12-year-old British girl on the Internet. He was jailed for four and half years by Manchester Crown Court in April 2004.
An overhaul of the law saw increased penalties for online paedophiles following the case of a former US marine who groomed a 12-year-old British girl on the Internet. He was jailed for four and half years by Manchester Crown Court in April 2004.
Serial paedophile Douglas Lindsell, 62, also posed as a child in chatrooms to lure 72 young girls to his home in Twickenham, so he could molest them. He was jailed in 2003.
“Arming children and their parents with good, practical advice is crucial to winning the battle against child sex offenders,” said Mr. Coaker.
A. Find synonyms in the text for the following words:
a) consequences
b) go to
c) carried out
d) established
e) adjustment
f) essential
B. Answer the following questions.
a) What kind of lessons will be given in every secondary school in Britain?
b) What do these lessons consist of?
c) Who will run those lessons?
d) How can the website referred to in the text help children?
e) Why does the Government back this service?
C. This is a reader’s opinion on the article you have just read. Write a small paragraph stating whether you agree or disagree with him.
This is definitely a step in the right direction but it’s the parents who really need education on the dangers of the Net. Most “grooming” takes place when children are surfing at home. It’s very irresponsible just to let children have PCs in their bedrooms and have no way of monitoring what they are looking at/ I suspect these lessons will have little impact – just as sex education lessons at school have had no impact on reducing teenage pregnancies.
Sean, Epsom

 Lesson 44.
Lesson 44.
1. SPEAKING
Comment on the cartoon:
2.  READING
READING
Read the texts below :
Text A
21st-century love
Women used to drop handkerchiefs as a way of getting men’s attention. And ... men used to pick them up so they had an excuse to talk to women.
That was at the beginning of the last century. Now it’s a completely different world!
E-mails and e-females find love
It doesn’t matter whether you have designer clothes or not, you don’t have to have your hair done and you can meet people 24/7. Shy people or those who wish someone would take time to get to know their personality, welcome online love. But cyberspace can be a dangerous place. American teen Carol was 13 when she met «Frank» in a chatroom, he said he was a 23-year-old student from California. Carol got used to confiding in « Frank» who pestered her to meet up with him. A few months later, she agreed to do it. « Frank» was a sex offender who attacked her.
Carol had a bad experience but it doesn’t have to be like that and to prevent this from happening all you have to do it to follow some simple safety tips:
· Never give important information about yourself to strangers on the Net and use an e-mail address that ensures nobody has these details.
· Be cautious about anyone who asks you to keep any kid of friendship secret.
· If you do arrange to meet anyone, make sure you stay in a public place.
· Avoid falling head over heels in love with anyone you’ve never met. You don’t actually know them!
A. Answer these questions on the text :
a) According to the text, which are the positive and negative aspects of cyberlove ?
b) Do you agree with them ? explain why/why not.
Text B Teens talk about cyberlove
 I personally wouldn’t go for online love but my sister did. It was a major drama. She e-mailed him, then phoned him, then ran off with him! After a couple of months they got married. Did I mention that he was Chinese and has never left his country? Well, that’s what I call a « cyber miracle».
Laura, 16 I personally wouldn’t go for online love but my sister did. It was a major drama. She e-mailed him, then phoned him, then ran off with him! After a couple of months they got married. Did I mention that he was Chinese and has never left his country? Well, that’s what I call a « cyber miracle».
Laura, 16
|  I know quite a few girls but if you are shy or live in an area where you don’t know a lot of girls, e-mails dating would be a good thing to do. You don’t have to marry them! You can just flirt a bit.
Tom, 17 I know quite a few girls but if you are shy or live in an area where you don’t know a lot of girls, e-mails dating would be a good thing to do. You don’t have to marry them! You can just flirt a bit.
Tom, 17
|
 I suppose the Internet is quite a good way of getting to know the person before you meet her to go on a date. I use the phone more than the e-mail. To tell the truth, I’m a phonaholic.
Rob, 16 I suppose the Internet is quite a good way of getting to know the person before you meet her to go on a date. I use the phone more than the e-mail. To tell the truth, I’m a phonaholic.
Rob, 16
|  You hear too many scary stories about online dating. Anyway, I’d want to go out with the person properly and get to know him by talking. I know it’s a stereotype but I imagine a real geek when I think of dating online.
Sarah, 15 You hear too many scary stories about online dating. Anyway, I’d want to go out with the person properly and get to know him by talking. I know it’s a stereotype but I imagine a real geek when I think of dating online.
Sarah, 15
|
B. Laura, Tom, Rob or Sarah? Who says what?
a) The Internet is a good way to approach people.
b) A family member got involved with someone online.
c) It’s better to know people personally.
d) It is said that online dating can be a dangerous thing.
e) Sending e-mails allows you to flirt a bit without having to build a serious relationship.
f) People who go for cyberlove are believed to be netaholic.
g) I spend a lot of time talking on the phone
3.  READING
READING
Read the text and complete it with the missing words given below.
You’ve Got Mail is a film that focuses on how two people can get easily when they are online without knowing that they are actually rivals in the business world.
|

 Meg Ryan _(a)_ Kathleen Kelly who is involved with Frank Navasky (Greg Kinnear). _(b)_ Frank, as a newspaper writer for the New York Observer, is devoted to the typewriter, Kathleen prefers her _(c)_ and logging into her AOL e-mail _(d)_. There, using the avatar Shopgirl, Kathleen communicates with NY152. This is the avatar for Joe Fox (Tom Hanks). Joe _(e)_ to the Fox family who runs a chain of “mega” bookstores, Fox Books, Kathleen, on the other hand, runs the independent bookstore, The Shop Around The Corner, that her mother ran before her. The central _(f)_ of the film revolves around the _(g)_ of Kathleen and Joe to interact well in _(h)_ while they are business competitors in the “real world”.
Meg Ryan _(a)_ Kathleen Kelly who is involved with Frank Navasky (Greg Kinnear). _(b)_ Frank, as a newspaper writer for the New York Observer, is devoted to the typewriter, Kathleen prefers her _(c)_ and logging into her AOL e-mail _(d)_. There, using the avatar Shopgirl, Kathleen communicates with NY152. This is the avatar for Joe Fox (Tom Hanks). Joe _(e)_ to the Fox family who runs a chain of “mega” bookstores, Fox Books, Kathleen, on the other hand, runs the independent bookstore, The Shop Around The Corner, that her mother ran before her. The central _(f)_ of the film revolves around the _(g)_ of Kathleen and Joe to interact well in _(h)_ while they are business competitors in the “real world”.
A. Now answer the following questions:
a) What does Frank Navasky do?
b) What’s Kathleen’s favourite hobby?
c) Explain the meaning of the word avatar?
d) Who is Joe Fox?
e) Are Joe and Kathleen on the same business? Which?
f) What’s the difference between their relationship online and their relationship in the “real world”?
g) How do you think the story ends?
4. ACRONYMS
Match the acronyms with the corresponding word/expression.
An acronym is an abbreviation of several words in such a way that the abbreviation itself forms a pronounceable word.
| Acronyms | Word/Expression |
| 1. 4ward 2. cos 3. XX 4. ur 5. BF 6. FYI 7. LMK 8. JK 9. OBTW 10. H | A. Hug B. Just kidding C. Boyfriend D. Let me know E. Forward F. Oh, by the way G. You are H. For your information I. Cause/Because J. Kisses |
5. 
READING
Read the text.
With the development of technology and everyone using computers and the Internet on a daily basis, you want to make sure that what you send is well-received. That is where Netiquette comes in. netiquette is a set of rules for behaving properly online. Just like when you visit a new country and must follow their rules, the same applies for cyberspace. In order not to offend or be offended by the people you’re interacting with online, you must follow cyberspace rules.
When the Internet was first created, it was mostly used by educational and research departments. At that time, the number of users was very low. The original users of the Internet were very ethical and set up a system of rules for e-mailing and discussion groups. The purpose of these rules was to keep some order and respect while communicating with others over the Net.
With the growing number of users, it is important to keep these guidelines in mind. While netiquette might at first appear as the rules of cyberspace, most take them as simple recommendations. Here are some of these rules.
· Do not write in upper case only. This appears as if you are shouting.
· Do not send abusive messages.
· If you want to send a big file, ask the recipient if it’s OK.
· If you’re in a hurry, you can still be polite by using abbreviations such as WBS for write back soon.
For whatever reason you are sending an e-mail, whether it is personal or work-related, be sure to always remain courteous. Remember that the Internet is a public forum and you never know who will read your message. Before sending something, ask yourself “How would I feel if I receive this message?”
A.Mark statements T (true) and F (false).
1. Mainly educational and research facilities used the Internet at first.
2. Netiquette does not allow any upper case letters.
3. The number of people using the Internet is increasing.
4. Insulting someone through e-mail is not permitted.
5. You don’t need to ask permission to send big files.
B.Choose the sentence which best summarizes the text.
1. Netiquette has been around for many years.
2. Netiquette is a polite method of online communication.
3. Netiquette was first used many years ago.
4. Netiquette is growing in popularity.
C.Explain the meaning of the following phrases:
1. well-received (line 2)
2. comes in (line 3)
3. keep these guidelines in mind (line 12)
4. abusive messages (line 16)
5. public forum (line 21)
D.Fill in the gaps using the words in bold from the text.
1. Her parents raised her to be a very …. young woman.
2. The student did not meet the … standards of the school and was expelled.
3. Organ donor … are put on a long waiting list.
4. E-mail is an … for electronic mail.
5. The social worker made some very good … to help deal with bullying.
6. The …. of the charity event was to raise money for the poor.
E.Answer the questions.
5. What could happen if you are impolite online?
6. What benefits are there to using netiquette?
6. EMOTICONS
Do you use emoticons?

 These are called emoticons. Use them when you want to make a point or make sure that your message is understood in the “emotion” you want.
These are called emoticons. Use them when you want to make a point or make sure that your message is understood in the “emotion” you want.
:-) Your basic smiley. This smiley is used to inflect a sarcastic or joking statement.
 ;-) Wink (something said tongue-in-cheek)
;-) Wink (something said tongue-in-cheek)
 :-( Sad, disappointed face.
:-( Sad, disappointed face.
‹:-ᴏ “Eeek!”
:’-( User is crying.
7. THE FUTURE OF EMAILING
What do teenagers really think of Email? Study the chart and express your thought about the future of emailing.

Date: 2015-01-29; view: 4096
| <== previous page | | | next page ==> |
| A. Complete the labels for these pictures. | | | Session n°2 (Tuesday, June 11th) : Basics in structural Geology |