
CATEGORIES:
BiologyChemistryConstructionCultureEcologyEconomyElectronicsFinanceGeographyHistoryInformaticsLawMathematicsMechanicsMedicineOtherPedagogyPhilosophyPhysicsPolicyPsychologySociologySportTourism
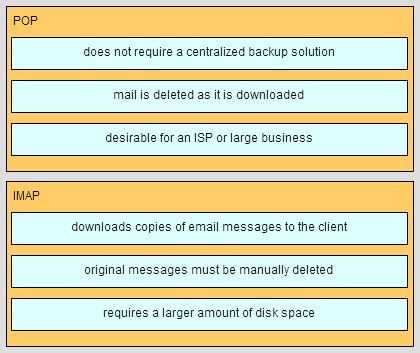
Match each characteristic to the appropriate email protocol. (Not all options are used.)
91. A host is accessing a Telnet server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Choose three.)
· regenerating data signals*
· acting as a client or a server
· providing a channel over which messages travel
· applying security settings to control the flow of data*
· notifying other devices when errors occur*
· serving as the source or destination of the messages
92. Refer to the exhibit. Which area would most likely be an extranet for the company network that is shown?
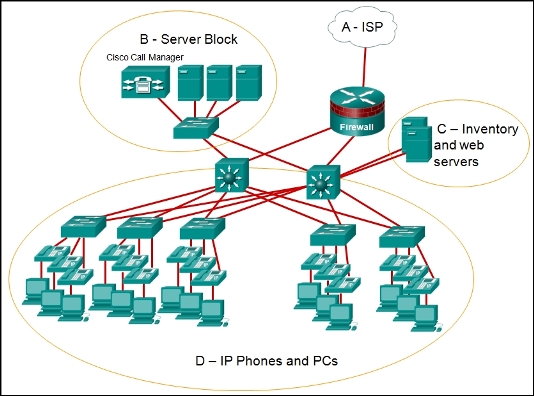
· area A
· area B
· area C*
· area D
93. What is the purpose of having a converged network?
· to provide high speed connectivity to all end devices
· to make sure that all types of data packets will be treated equally
· to achieve fault tolerance and high availability of data network infrastructure devices
· to reduce the cost of deploying and maintaining the communication infrastructure*
94. Three office workers are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other office workers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
· audio conference, financial transactions, web page*
· financial transactions, web page, audio conference
· audio conference, web page, financial transactions
· financial transactions, audio conference, web page
95. During normal operation, from which location do most Cisco switches and routers run the IOS?
· RAM*
· flash
· NVRAM
· disk drive
96. A network administrator is making changes to the configuration of a router. After making the changes and verifying the results, the administrator issues the copy running-config startup-config command. What will happen after this command executes?
· The configuration will be copied to flash.
· The configuration will load when the router is restarted.*
· The new configuration file will replace the IOS file.
· The changes will be lost when the router restarts.
97. What information does the loopback test provide?
· The TCP/IP stack on the device is working correctly.*
· The device has end-to-end connectivity.
· DHCP is working correctly.
· The Ethernet cable is working correctly.
· The device has the correct IP address on the network.
98. What is a characteristic of the LLC sublayer?
· It provides the logical addressing required that identifies the device.
· It provides delimitation of data according to the physical signaling requirements of the medium.
· It places information in the frame allowing multiple Layer 3 protocols to use the same network interface and media.*
· It defines software processes that provide services to the physical layer.
99. What method is used to manage contention-based access on a wireless network?
· CSMA/CD
· priority ordering
· CSMA/CA*
· token passing
100. What happens when a switch receives a frame and the calculated CRC value is different than the value that is in the FCS field?
· The switch places the new CRC value in the FCS field and forwards the frame.
· The switch notifies the source of the bad frame.
· The switch drops the frame.*
· The switch floods the frame to all ports except the port through which the frame arrived to notify the hosts of the error.
101. Which destination address is used in an ARP request frame?
· 0.0.0.0
· 255.255.255.255
· FFFF.FFFF.FFFF*
· 127.0.0.1
· 01-00-5E-00-AA-23
102. What is the auto-MDIX feature on a switch?
· the automatic configuration of an interface for 10/100/1000 Mb/s operation
· the automatic configuration of an interface for a straight-through or a crossover Ethernet cable connection*
· the automatic configuration of full-duplex operation over a single Ethernet copper or optical cable
· the ability to turn a switch interface on or off accordingly if an active connection is detected
103. Which frame forwarding method receives the entire frame and performs a CRC check to detect errors before forwarding the frame?
· cut-through switching
· store-and-forward switching*
· fragment-free switching
· fast-forward switching
104. What are the two main components of Cisco Express Forwarding (CEF)? (Choose two.)
· adjacency tables
· MAC-address tables
· routing tables*
· ARP tables*
· forwarding information base (FIB)
105. Which statement describes the sequence of processes executed by a router when it receives a packet from a host to be delivered to a host on another network?
· It receives the packet and forwards it directly to the destination host.
· It de-encapsulates the packet, selects the appropriate path, and encapsulates the packet to forward it toward*
· the destination host.*
· It de-encapsulates the packet and forwards it toward the destination host.
· It selects the path and forwards it toward the destination host.
106. Which technology provides a solution to IPv4 address depletion by allowing multiple devices to share one public IP address?
· ARP
· DNS
· NAT*
· SMB
· DHCP
· HTTP
107. Refer to the exhibit. Router R1 has two interfaces that were configured with correct IP addresses and subnet masks. Why does the show ip route command output not display any information about the directly connected networks??
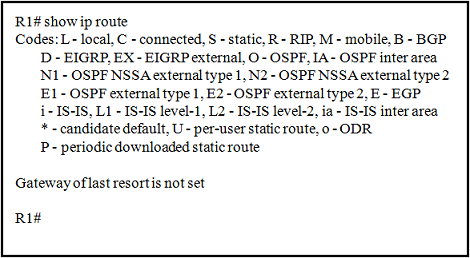
· The directly connected networks have to be created manually to be displayed in the routing table.
· The routing table will only display information about these networks when the router receives a packet.
· The no shutdown command was not issued on these interfaces.*
· The gateway of last resort was not configured.
108. What happens when part of an Internet television transmission is not delivered to the destination?
· A delivery failure message is sent to the source host.
· The part of the television transmission that was lost is re-sent.
· The entire transmission is re-sent.
· The transmission continues without the missing portion.*
109. Which three statements characterize the transport layer protocols? (Choose three.)
· TCP and UDP port numbers are used by application layer protocols.*
· TCP uses port numbers to provide reliable transportation of IP packets.
· UDP uses windowing and acknowledgments for reliable transfer of data.
· TCP uses windowing and sequencing to provide reliable transfer of data.*
· TCP is a connection-oriented protocol. UDP is a connectionless protocol.*
110. A user opens three browsers on the same PC to access www.cisco.com to search for certification course information. The Cisco web server sends a datagram as a reply to the request from one of the web browsers. Which information is used by the TCP/IP protocol stack in the PC to identify the destination web browser?
· the destination IP address
· the destination port number*
· the source IP address
· the source port number
111. Which statement is true regarding the UDP client process during a session with a server?
· Datagrams that arrive in a different order than that in which they were sent are not placed in order.*
· A session must be established before datagrams can be exchanged.
· A three-way handshake takes place before the transmission of data begins.
· Application servers have to use port numbers above 1024 in order to be UDP capable.
112. Which two components are configured via software in order for a PC to participate in a network environment? (Choose two.)
· MAC address
· IP address*
· kernel
· shell
· subnet mask*
113. What are three characteristics of multicast transmission? (Choose three.)
· The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
· A single packet can be sent to a group of hosts.*
· Multicast transmission can be used by routers to exchange routing information.*
· Routers will not forward multicast addresses in the range of 224.0.0.0 to 224.0.0.255.*
· Computers use multicast transmission to request IPv4 addresses.
· Multicast messages map lower layer addresses to upper layer addresses.
114. Which two reasons generally make DHCP the preferred method of assigning IP addresses to hosts on large networks? (Choose two.)
· It eliminates most address configuration errors.*
· It ensures that addresses are only applied to devices that require a permanent address.
· It guarantees that every device that needs an address will get one.
· It provides an address only to devices that are authorized to be connected to the network.
· It reduces the burden on network support staff.*
115. What is the subnet address for the address 2001:DB8:BC15:A:12AB::1/64?
· 2001:DB8:BC15::0
· 2001:DB8:BC15:A::0*
· 2001:DB8:BC15:A:1::1
· 2001:DB8:BC15:A:12::0
116. Which two tasks are functions of the presentation layer? (Choose two.)
· compression*
· addressing
· encryption*
· session control
· authentication
117. What is the purpose of the network security authentication function?
· to require users to prove who they are*
· to determine which resources a user can access
· to keep track of the actions of a user
· to provide challenge and response questions
118. Which type of wireless security makes use of dynamic encryption keys each time a client associates with an AP?
· EAP
· PSK
· WEP
· WPA*
Fill in the blank.
Date: 2015-12-18; view: 4580