CATEGORIES:
BiologyChemistryConstructionCultureEcologyEconomyElectronicsFinanceGeographyHistoryInformaticsLawMathematicsMechanicsMedicineOtherPedagogyPhilosophyPhysicsPolicyPsychologySociologySportTourism
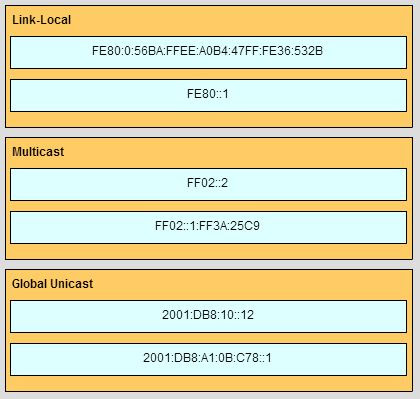
Match the phases to their correct stage in the router bootup process. (Not all options are used.)Match the IPv6 address to the IPv6 address type. (Not all options are used.)
51. What two preconfigured settings that affect security are found on most new wireless routers? (Choose two.) · broadcast SSID* · MAC filtering enabled · WEP encryption enabled · PSK authentication required · default administrator password* 52. Which type of wireless security generates dynamic encryption keys each time a client associates with an AP? · EAP · PSK · WEP · WPA* Fill in the blank. TFTP is a best-effort, connectionless application layer protocol that is used to transfer files. 54. Which two components are necessary for a wireless client to be installed on a WLAN? (Choose two.) · media · wireless NIC* · custom adapter · crossover cable · wireless bridge · wireless client software* 55. Consider the following range of addresses: 2001:0DB8:BC15:00A0:0000:: 2001:0DB8:BC15:00A1:0000:: 2001:0DB8:BC15:00A2:0000:: … 2001:0DB8:BC15:00AF:0000:: The prefix-length for the range of addresses is /60 . Match the phases to their correct stage in the router bootup process. (Not all options are used.)
· Stage 1 – perform the post · Stage 2 – load the bootstrap program · Stage 3 – Locate and load the Cisco IOS · Stage 4 – locate and load the configuration file
57. A host is accessing an FTP server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Choose three.) · regenerating data signals* · acting as a client or a server · providing a channel over which messages travel · applying security settings to control the flow of data* · notifying other devices when errors occur* · serving as the source or destination of the messages 58. When is a dial-up connection used to connect to an ISP? · when a cellular telephone provides the service · when a high-speed connection is provided over a cable TV network · when a satellite dish is used · when a regular telephone line is used* 59. On a school network, students are surfing the web, searching the library database, and attending an audio conference with their sister school in Japan. If network traffic is prioritized with QoS, how will the traffic be classified from highest priority to lowest priority? · audio conference, database, HTTP* · database, HTTP, audio conference · audio conference, HTTP, database · database, audio conference, HTTP 60. During normal operation, from which location do most Cisco routers run the IOS? · RAM* · flash · NVRAM · disk drive 61. Which connection provides a secure CLI session with encryption to a Cisco switch? · a console connection · an AUX connection · a Telnet connection · an SSH connection* 62. Which keys act as a hot key combination that is used to interrupt an IOS process? · Ctrl-Shift-X · Ctrl-Shift-6* · Ctrl-Z · Ctrl-C 63. Refer to the exhibit. An administrator wants to change the name of a brand new switch, using the hostname command as shown. What prompt will display after the command is issued??
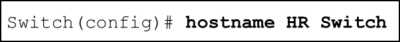
· HR Switch(config)#? · Switch(config)#?* · HRSwitch(config)#? · HR(config)#? · Switch# 64. After making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command? · The new configuration will be stored in flash memory. · The new configuration will be loaded if the switch is restarted.* · The current IOS file will be replaced with the newly configured file. · The configuration changes will be removed and the original configuration will be restored. 65. On which switch interface would an administrator configure an IP address so that the switch can be managed remotely? · FastEthernet0/1 · VLAN 1* · vty 0 · console 0 66. A technician uses the ping 127.0.0.1 command. What is the technician testing? · the TCP/IP stack on a network host* · connectivity between two adjacent Cisco devices · connectivity between a PC and the default gateway · connectivity between two PCs on the same network · physical connectivity of a particular PC and the network 67. What is the correct order for PDU encapsulation?
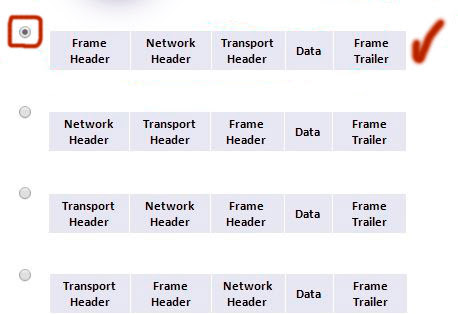
68. Which device should be used for enabling a host to communicate with another host on a different network? · switch · hub · router* · host 69. A network technician is measuring the transfer of bits across the company backbone for a mission critical application. The technician notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.) · the amount of traffic that is currently crossing the network* · the sophistication of the encapsulation method applied to the data · the type of traffic that is crossing the network* · the latency that is created by the number of network devices that the data is crossing* · the bandwidth of the WAN connection to the Internet · the reliability of the gigabit Ethernet infrastructure of the backbone 70. Which characteristics describe fiber optic cable? (Choose two.) · It is not affected by EMI or RFI.* · Each pair of cables is wrapped in metallic foil. · It combines the technique of cancellation, shielding and twisting to protect data. · It has a maximum speed of 100 Mbps. · It is the most expensive type of LAN cabling* 71. What are two features of a physical, star network topology? (Choose two.) · It is straightforward to troubleshoot.* · End devices are connected together by a bus. · It is easy to add and remove end devices.* · All end devices are connected in a chain to each other. · Each end system is connected to its respective neighbor. 72. A frame is transmitted from one networking device to another. Why does the receiving device check the FCS field in the frame? · to determine the physical address of the sending device · to verify the network layer protocol information · to compare the interface media type between the sending and receiving ends · to check the frame for possible transmission errors* · to verify that the frame destination matches the MAC address of the receiving device 73. What will a Layer 2 switch do when the destination MAC address of a received frame is not in the MAC table? · It initiates an ARP request. · It broadcasts the frame out of all ports on the switch. · It notifies the sending host that the frame cannot be delivered. · It forwards the frame out of all ports except for the port at which the frame was received.* 74. Which switching method has the lowest level of latency? · cut-through · store-and-forward · fragment-free · fast-forward* 75. Which parameter does the router use to choose the path to the destination when there are multiple routes available? · the lower metric value that is associated with the destination network* · the lower gateway IP address to get to the destination network · the higher metric value that is associated with the destination network · the higher gateway IP address to get to the destination network 76. Which two statements describe the functions or characteristics of ROM in a router? (Choose two.) · stores routing tables · allows software to be updated without replacing pluggable chips on the motherboard · maintains instructions for POST diagnostics* · holds ARP cache · stores bootstrap program* 77. Which statement describes a characteristic of the Cisco router management ports? · A console port is used for remote management of the router. · A console port is not used for packet forwarding.* · Serial and DSL interfaces are types of management ports. · Each Cisco router has a LED indicator to provide information about the status of the management ports. 78. What happens when part of an Internet radio transmission is not delivered to the destination? · A delivery failure message is sent to the source host. · The part of the radio transmission that was lost is re-sent. · The entire transmission is re-sent. · The transmission continues without the missing portion.* 79. What is the dotted decimal representation of the IPv4 address 11001011.00000000.01110001.11010011? · 192.0.2.199 · 198.51.100.201 · 203.0.113.211* · 209.165.201.223 80. Which three IP addresses are private ? (Choose three.) · 10.20.30.1* · 172.32.5.2 · 192.167.10.10 · 172.30.5.3* · 192.168.5.5* · 224.6.6.6 81. What types of addresses make up the majority of addresses within the /8 block IPv4 bit space? · private addresses · public addresses* · multicast addresses · experimental addresses 82. Refer to the exhibit. What is the maximum TTL value that is used to reach the destination www.cisco.com??
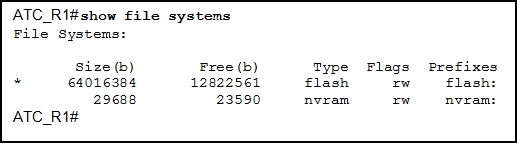
· 11 · 12 · 13* · 14 83. A company has a network address of 192.168.1.64 with a subnet mask of 255.255.255.192. The company wants to create two subnetworks that would contain 10 hosts and 18 hosts respectively. Which two networks would achieve that? (Choose two.) · 192.168.1.16/28 · 192.168.1.64/27* · 192.168.1.128/27 · 192.168.1.96/28* · 192.168.1.192/28 84. In a network that uses IPv4, what prefix would best fit a subnet containing 100 hosts? · /23 · /24 · /25* · /26 85. Which protocol supports rapid delivery of streaming media? · Transmission Control Protocol · Real-Time Transport Protocol* · Secure File Transfer Protocol · Video over Internet Protocol 86. Why would a network administrator use the tracert utility? · to determine the active TCP connections on a PC · to check information about a DNS name in the DNS server · to identify where a packet was lost or delayed on a network* · to display the IP address, default gateway, and DNS server address for a PC 87. Refer to the exhibit. What is the significance of the asterisk (*) in the exhibited output?
· The asterisk shows which file system was used to boot the system. · The asterisk designates which file system is the default file system.* · An asterisk indicates that the file system is bootable. · An asterisk designates that the file system has at least one file that uses that file system. 88. Which WLAN security protocol generates a new dynamic key each time a client establishes a connection with the AP? · EAP · PSK · WEP · WPA* Fill in the blank. Point-to-point communications where both devices can transmit and receive on the medium at the same time are known as full-duplex. Date: 2015-12-18; view: 3695 |